Conclusion organizations are finding themselves under the pressure of being forced to react quickly to the dynamically increasing number of cybersecurity threats.
Conclusion of cyber security project.
The cybersecurity workforce encompasses a variety of contexts roles and occupations and is too broad and diverse to be treated as a single occupation or profession.
The hacker s identity is ranged between 12 years young to 67years old.
Whether and how to professionalize will vary according to role and context.
For the most part cybersecurity problems result from the inherent nature of information technology it the complexity of information technology systems and human fallibility in making judgments about what actions and information are safe or unsafe from a cybersecurity perspective especially when such actions and information are highly complex.
Overall existing multilateral and regional legal instruments and national laws vary in terms of thematic content and extent of coverage of criminalization investigative measures and powers digital evidence regulation and risk and jurisdiction and international.
This software protects.
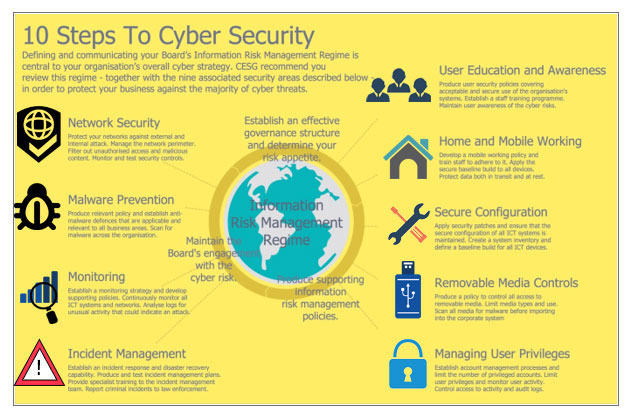
Since the attackers have been using an attack life cycle organizations have also been forced to come up with a vulnerability management life cycle.
For cyber security projects to be effective it and security professionals need to implement a solid project management plan working with a team including an experienced project manager can help ensure that projects are executed smoothly stay on budget completed within time frame and that nothing falls through the cracks in the course of implementation which can make such solution to be vulnerable in the future.
Cybersecurity means protecting data networks programs and other information from unauthorized or unattended access destruction or change.
This module is a resource for lecturers conclusion several international treaties have been implemented relating to cybercrime.
12 ways to protect your business from a cyber security attack april 10 2018 may 1 2020 by monica morris cyber security it network security 0 comment.
Crimes by computer vary and they don t always occur behind the computer but they executed by computer.
Conclusion the future of cybersecurity will in one sense be like the present.
For data protection many companies develop software.